This is a current events re-post from CyberNews
North Korean hackers build “shiny new” macOS malware, but get hacked themselves

North Korean attackers are using a new macOS malware kit to target developers, executives, and other specialists in high-value environments like fintech and crypto. It would be a shame if someone took over their Telegram bots and flooded their infrastructure with junk.
Mauro Eldritch, an offensive security expert and the founder of BCA LTD, is warning of a malicious campaign actively targeting macOS users with new malware. Coincidentally, hackers themselves got hacked.
The campaign reshuffles old social engineering tactics – North Korean hackers hunt for business leaders on Telegram and elsewhere and invite them to discuss various business projects on fake Zoom, Teams, or Meet meetings.
At the start of the call, simulated technical problems prompt victims “to copy and paste a fix into their terminal” – a variation of the ClickFix attack, which tricks users into downloading and running malware themselves.
The new macOS malware, attributed to the North Korean Lazarus group, grabs credentials, browser sessions, macOS Keychain data, and beams it using Telegram to an attacker-controlled server (C2).
The malware is badly written, with certain components entering infinite loops that may expose its presence due to system resource starvation,” reads a blog post on ANY.RUN, an interactive malware analysis sandbox platform.
Despite many bugs, the malware still does the job, and hackers get away with stolen data before victims realize. A single compromised macOS device can result in wide access to internal systems, crypto assets, and production environments.
Hackers’ “worst weekend outage of the year”
The discovery of the new malware coincided with the North Korean threat group’s infrastructure being hacked. Eldritch’s blog was the first to provide details of how this could have happened.
The researcher discovered two critical vulnerabilities in the attackers’ C2 infrastructure.
One folder on the server, used by the malware to exfiltrate data, allowed unrestricted file uploads without any authentication, “as long as the expected User-Agent and file format are respected.”
“This could allow virtually anyone to impersonate the malware and flood their infrastructure with mass-produced files until their services become unusable, due to file pollution, server saturation, or account suspension, whichever comes first,” the cheeky post reads.
The screenshot, showing how the server could be brought down by a few lines of code, looping the same forged request over and over, would look “something like this:”
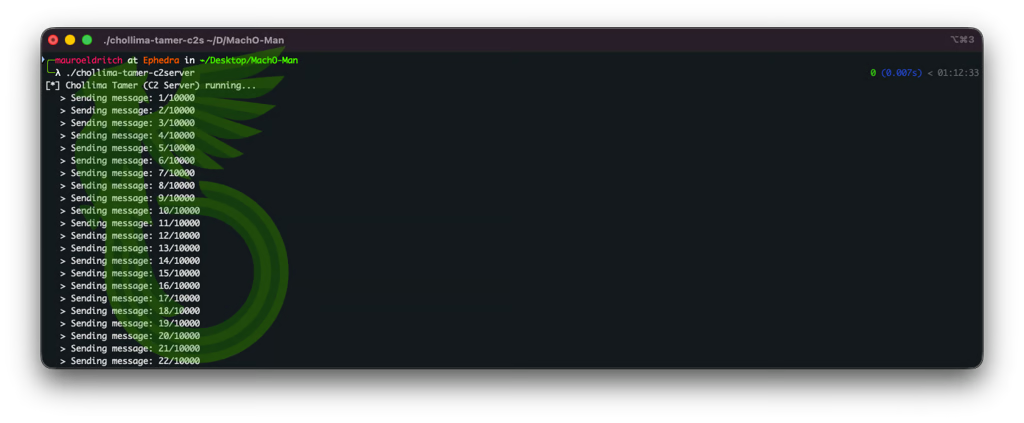
Image by Mauro Eldritch.
Another “artist’s impression” demonstrates the server no longer responding to requests, if the cyberattack were to succeed:
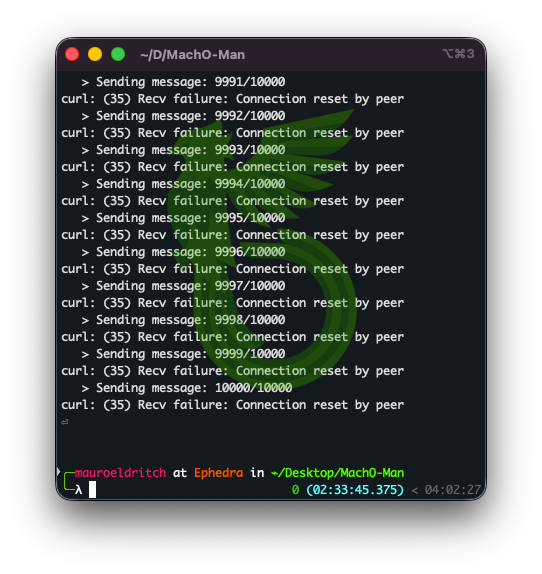
Image by Mauro Eldritch.
The second critical flaw in Lazarus’ attack chain was its reliance on a Telegram bot for exfiltration. Malware had the bot’s API token exposed, which is essentially the administrator’s key, allowing it to read and send messages on the bot’s behalf.
Apparently, North Korean hackers started suffering from spam flooding both incoming and outgoing channels.
“But there’s more! This key allows anyone to identify the bot owner or creator,” Eldritch writes.
The post responsibly discloses the Telegram account used by the DPRK hackers.
“By combining these two C2 vulnerabilities, we could easily turn this into a mass spamming campaign, flooding both the bot and the C2 infrastructure and effectively causing their worst weekend outage of the year,” the author concluded.
However, the researchers warn that despite the setbacks, North Korean attackers will not stop.
The malware is still dangerous
North Korean attackers rely on phishing and convincing social engineering attacks to run their campaigns. The familiar and urgent scenarios lower suspicion, increasing the chances of interaction. When users run malicious commands themselves, they do not trigger traditional security tools.
By the time victims realize they’ve been tricked, the attackers are already gone: they’ve collected credentials, browser sessions, system secrets, and more.
The researcher published a detailed technical report on the new macOS malware on ANY.RUN, which also shared a live sandbox analysis, demonstrating how the kit works.
Eldritch dubbed the malware “Mach-O Man” for the use of native macOS Mach-O binaries.
Image by Cybernews.
The malware has four stages in total.
Initial command, that users paste into the terminal hoping to fix issues on fake Zoom, Meets, or Teams calls, pulls and executes a “stager.” This initial component comes as a ‘teamsSDK.bin’ executable file. It downloads a fake app impersonating Zoom, Meets, Google, or System, only differing in visual cues.
The app prompts the user for their password a few times, always indicating that the first few attempts were incorrect.
The second stage – the profiler– is downloaded in the background. This binary registers the victim’s computer with the command and control (C2) server and sends system details, network configuration, processes, browser extensions, etc.
The third stage is a persistence mechanism, disguised as OneDrive. The malware sets it up as a startup item, reinvoking the kit at every login. Before moving to the final stage, it tidies up, deleting previous ZIP files and fake apps.
The fourth stage is the main component – the stealer, capable of capturing browser extension data, stored browser credentials and cookies (typically kept in SQLite databases), macOS Keychain entries, and other files of interest. Malware archives the data in a ZIP file, exfiltrates it via a Telegram bot, and then self-deletes.
This article was ripped and re posted from: CyberNews without all the adware by Graystone to provide you current news without the risk of well-poisoning drive by malware. All content © the respective creator via their original site.
Graystone is just sharing just the news.


Comments are closed